Cyberstalking Facts
and
Types of Cyberstalkers
Cyberstalking Facts: The stalker & cyberstalker profile involves multiple descriptions, definitions and dimensions. With the advent of Information and Communications Technology, cyberstalking has grown to become a concern for law enforcement and anyone engaged in online activities.
The typologies of stalkers are theoretical descriptions shared by both the cyber and physical stalkers. The goal of victim prevention is to first understand their rationale for acting as a predator and then develop strategies to prevent becoming a victim. Learning to profile and predict the stalker & cyberstalker reduces the predator’s objective of causing you or your loved ones psychological and physical harm.
Stalking is a behavior wherein a person willfully and repeatedly engages in conduct directed towards another person who, if known by the victim, causes significant concern and fear. The predator that initiates and sustains the stalking behavior(s) may or may not recognize he/she is causing their victim serious alarm, perceptual torment and the unfortunate experience of being terrorized.
Stalking involves one person’s obsessive behavior toward another person. Initially, stalking usually takes the form of annoying, threatening or obscene telephone calls, emails or letters. During this period, the victim views the stalker’s actions as more of a form of harassment as opposed to an escalating dangerous situation. Once the harassment stage has been established, it is during this period that the potential victim needs to contact law enforcement. It is also crucial to begin keeping a written log documenting each time the stalker makes contact.
Psychiatrists, psychologists, and other mental health professionals view most stalkers as suffering from a psychiatric illness(s) causing them to be psychotic or delusional. When not deemed as psychotic, stalkers are considered plagued by some type of personality disorder or fueled by unique psychological factors. In the most severe cases, the stalker is defined as a predatory stalker or sociopath.
Whatever the psychological rationale may be, the stalker rarely comprehends the fear he/she is causing the other person. Blinded by his/her motivations to stalk someone in the first place causes them to lose sight of the fear and terror they are causing. When anger, rage and hostility towards the victim are involved, the stalker is fully aware of the anguish he/she is causing, but feels the victim is deserving of the fear or simply does not care. In 1999, Australian stalking expert, Dr. Paul Mullen, and a group of investigators identified five types of stalkers, which remain applicable today for stalkers and cyberstalkers and as follows:
Stalker & Cyberstalking Typologies
Rejected Stalkers/Cyberstalkers: This type of stalker/cyberstalker is motivated to pursue their victim in an attempt to reverse what they perceive as a wrongful set of circumstances causing a prior divorce, separation or termination of a relationship. These offenders either feel misunderstood hoping to reverse the breakup or feel angry and seeking revenge because their attempts at reconciliation with the victim have failed in the past.
Resentful Stalkers/Cyberstalkers: This type of stalker/cyberstalker can be dangerous given their perceived motivation for stalking. Resentful stalkers/cyberstalkers are fully aware the victim is cognizant of the stalking but continues to fulfill a distorted vendetta he/she feels is warranted. Fear and distress experienced by the victim are the goals of this type of stalker/cyberstalker. For this type of profile, the stalker/cyberstalker believes the victim both deserves and requires being frightened because they have caused them and/or others anguish and distress.
Intimacy Seekers: This type of stalker/cyberstalker does not have ill will towards their victim. They simply want a loving relationship with them. Intimacy seekers view their victims as their soulmate destined to be together at all costs. Within their mind, they believe it is their job and purpose to make sure the destiny of a loving relationship is fulfilled. Intimacy seeking stalkers/cyberstalkers are often the segment of men or women who target celebrities and public figures. Blinded by their distorted perceptions of a destined love, they lose sight of the distress and fear they are causing the person they target.
Incompetent Suitors: This type of stalker/cyberstalker is deeply enamored with their victim. Their interest in the target can reach a state of fixation whereby their entire waking life is focused on the endeavor of one day becoming a couple. They tend to lack social, communication or courting skills and may feel entitled that their fantasy of a loving relationship is inevitable. Feeling entitled and/or deserving of a relationship with the victim inspires the stalker/cyberstalker to gradually increase their frequency of contact. Although like the Intimacy Seeker stalker/cyberstalker, Incompetent Suitors are more gradual in their means and methods of contact.
Predatory Stalkers/Cyberstalkers: Of the six types, the predatory stalker/cyberstalker can be the most dangerous and determined. This type of stalker/cyberstalker is motivated by a perverted sexual need. They actively engage in planning an attack along with fantasizing about sexual acts with their victim. They do not have feelings of love for their victim, nor are they motivated by a belief in predestination. Their fuel to dominate and victimize resembles the psychopath experiencing little to no remorse for the welfare of their target.
Ghost Cyberstalkers: Not included in Dr. Mullen’s five stalker profiles, the ghost cyberstalker is unique to the Information Age. They are online assailants who their target cannot identify. Using Cyberstealth, the ghost cyberstalker inspires fear and/or repeatedly makes direct or indirect threats of physical harm. They can represent an amalgamation of the other five types, be a predatory troll or a sadistic online user with no connection to their victim. Ghost cyberstalkers rely upon the veil of anonymity afforded to all online users.
Understanding the types of stalker/cyberstalker and what motivates them is the first step in reducing the probability of becoming one of their victims. Unfortunately, many men, women and society in general minimize the stalker/cyberstalker profile and mistakenly view these people as “unfortunate souls looking for love.” What people fail to understand is most of these predators engaged in cyberstalking suffer troublesome psychiatric illnesses, psychological issues, or motivated by urges to sexually dominate their victim(s).
“Welcome to the unseemly and perverse world of cyberstalkers; the digitally depraved and malevolent iPredators.”
Michael Nuccitelli, Psy.D.
A growing number of states have cyberstalking, cyber harassment and cyberbullying laws and/or include Information and Communications Technology within their traditional stalking or harassment laws. Protecting minors from online bullying and harassment have led states to enact cyber bullying laws. Cyberstalking is the use of Information and Communications Technology to stalk and refers to a pattern of threatening or malicious behaviors. Cyberstalking may be considered the most dangerous of the three types of information and communications technology harassment, based on posing a credible threat of harm. Legal sanctions range from misdemeanors to felonies and vary by state.
Cyber harassment differs from cyberstalking in that does not involve a credible physical threat. Cyber harassment usually pertains to threatening or harassing messages using Information and Communications Technology to torment an individual, group or organization. Some states approach cyber harassment by including language addressing electronic communications in general harassment laws, while others have created stand-alone cyber harassment statutes.
Cyberbullying and cyber harassment are sometimes used interchangeably, but cyber bullying is used for electronic harassment or bullying among minors. Recent cyber bullying legislation reflects a trend of making school districts the policy enforcers of cyber bullying. As a result, statutes establish the infrastructure for schools to handle this issue by amending existing school anti-bullying policies to include cyber bullying and cyber harassment among school age children. Most of these state laws establish sanctions for all forms of cyber bullying on school property, school buses and official school functions.
However, some have also extended sanctions to include cyberbullying activities that originate off-campus, believing that activities off-campus can have a detrimental and disruptive effect on a child’s learning environment. The legal sanctions for cyberbullying range from misdemeanors to felonies with detention, suspension and expulsion from school.
Cyberbullying is a generic term used to define harmful, repeated and hostile online behavior intended to deprecate a targeted online user. Cyberbullying describes threatening or disparaging communications delivered through ICT. Whereas classic bullying typically involves face-to-face interactions and non-digital forms of communication, cyber bullying consists of information exchanged via ICT and may never involve face-to-face encounters.
Bullying or classic bullying is a term used to define recurrent and sustained verbal and/or physical attacks by a child, adolescent or adult towards others who are unable or unwilling to deescalate the engagement. It may involve verbal harassment, physical assault, coercion, intimidation, humiliation and taunting. Bullying is composed of a combination of four basic types of abuse: emotional, social, verbal and physical abuse. Despite variants in definition, bullying always involves the use of harassment, force or coercion to affect a targeted victim. Classic bullying requires face-to-face interactions within the repertoire of behaviors. Among the billions of online users, lurks a dangerous element the unsuspecting person may fall victim to. Cyberstalkers and online predators are two groups who access the Internet seeking harmful interactions. In most cyberstalking events, the assailant is termed an iPredator.
Three Free Educational Cyberstalking Assessment Links
Cyberstalking Prevention Checklist [CSPC]
iPredator Probability Inventory – Cyberstalking [IPI-CS]
Cyberstalker Identification Interview [CSII]
Stalking and Cyberstalking also falls under the theoretical construct of Dark Psychology, coined by this writer. Dark Psychology is the study of the human condition as it relates to the psychological nature of people to prey upon others. All of humanity has this potential to victimize other humans & living creatures. While many restrain or sublimate this tendency, some act upon these impulses.
Dark Psychology seeks to understand those thoughts, feelings and perceptions that lead to predatory behavior. Dark Psychology assumes that this production is purposive and has some rational, goal-oriented motivation 99% of the time. The remaining 1%, under Dark Psychology, is the brutal victimization of others without purposive intent or defined by evolutionary science or religious dogma.
With the advent of the internet, a unique environment now exists for Cyberstalkers and online predators. Millions of children, teens and adults create billions of internet exchanges daily. With the addition of cell phone and text messaging, the daily exchange number reaches billions. Digital technology, telecommunications and the cyberspace environment are now hunting grounds for online predators and iPredators.
Cyberstalking was predicted as inevitable for years, but only recently have parents, young people and community agencies started to focus on this growing problem. To exemplify how this warning has been explained for well over a decade, the Department of Justice (DOJ) authored and released the 1999 Report “Cyberstalking: A New Challenge for Law Enforcement and Industry“ and defined cyberstalking, the dangers to children and cyberstalking resources. In this report, the DOJ is not only thorough, but prophetic as well. They clearly stated the problems of cyberstalking and predicted the number of online predators would increase with each passing year.
It is many years later, and the DOJ was correct in their predictions. Although the resources they provide are all highly reputable with excellent information, Working to Halt Online Abuse (WHOA), National Center for Victims of Crime, Cyber Angels and National Cybercrime Training Partnership are four organizations with incredible resources and educational tools.
For those interested in furthering their knowledge base on cyberstalkers and online predators, the International Association of Computer Investigation (IACIS) is a reputable organization. Their mission as stated at their web site is “IACIS® is an international volunteer non-profit corporation composed of law enforcement professionals dedicated to education in the field of forensic computer science. IACIS members represent Federal, State, Local and International Law Enforcement professionals. Regular IACIS members have been trained in the forensic science of seizing and processing computer systems.”
Although expert associations like the DOJ and IACIS work to apprehend online predators, the number of cyber stalkers will continue to grow and it must be the citizens themselves to learn how to reduce their potential for becoming a future victim. The cyber stalker refers to a male, female or group of people who use the internet, e-mail, or any other electronic communications device to stalk another person. Stalking is defined as a behavior wherein a person willfully and repeatedly engages in conduct directed towards another person who, if known by the victim, can cause significant concern and fear.

Cyberstalking Examples
Stalking generally involves harassing or threatening behavior that an individual or group engages in repeatedly targeting a victim(s). Cyberstalking is the same but includes the methods of intimidation and harassment via information and communications technology. Cyberstalking consists of harassing and/or tormenting behaviors in the form of:
I. Electronic messaging such as classic emails, text messages and Twitter.
II. Spamming and/or sending threatening emails to the victim or victim’s family, friends or co-workers.
III. Posting the victim’s personal information such as name, address, phone numbers, and e-mail address online.
IV. Posting offensive comments in the victim’s name.
V. Creating and posting sexually explicit images of the victim or victim’s loved ones.
VI. Hacking into the victim’s computer, accounts and mobile devices.
VII. Subscribing the victim to pornography sites and unwanted advertising.
VIII. Attaching spyware to emails or installing it on the computer.
IX. Setting up websites that threaten the victim or encourage others to contact, harass or harm them.
X. Computer Monitoring Software, or “Spyware,” allows a cyberstalker to monitor computer and Internet activities and discover a victim’s efforts to escape or access help. This software can be installed remotely or by physically accessing the victim’s computer.
Most stalking laws in the United States require the offender(s) to make a credible threat of violence against the victim. In addition to directly threatening the victim with harm, family members who are threatened may also be grounds for arrest. Depending on state laws, the alleged stalker’s course of conduct can constitute an implied threat. The National Center for Victims of Crime is a dedicated association, which can assist locating and defining state stalking laws and how to proceed.
While some stalking and cyberstalking conduct involving annoying or bothersome behavior falls short of illegal stalking, these behaviors may be a prelude to more intense stalking and violence. The goal is to treat these actions as serious and not to minimize. Although these behaviors could be defined as harassment, the time to become proactive is when knowledge of these actions becomes apparent.
Cyberstalkers are often motivated by negative emotions or serious psychological factors. Psychiatric illness, obsession fixations, revenge, hate, anger and jealousy are common affective states fueling the cyber stalker. At times, the victim may not even know or ever meet the cyberstalker indicating another red flag of alert. Once aware of any indication of harassment or stalking has been initiated, the immediate next step is contacting local authorities. Although contacting local authorities may sound overblown or drastic, the potential outcome of not doing so may be far worse.
The methods the cyberstalker engages in ranges from novice to advanced. The more advanced they are in new electronic technology, the more proficient they become at targeting their victim. One of the methods few victims are aware of used by the cyberstalker is called cyber or digital surveillance. Cyber surveillance has both positive and negative applications. In the wrong hands, cyber surveillance can be deadly.
Also called Digitally Mediated Surveillance (DMS), this advanced technology is becoming increasingly prevalent and more accessible by those seeking to secure their environment and those seeking to spy on others. Each time a person goes online, text messages, or uses anything else involving electronic communications, they produce a growing stream of personal digital data of interest to unseen others. As DMS becomes more accessible to the general population, the more careful unsuspecting victims will have to be.
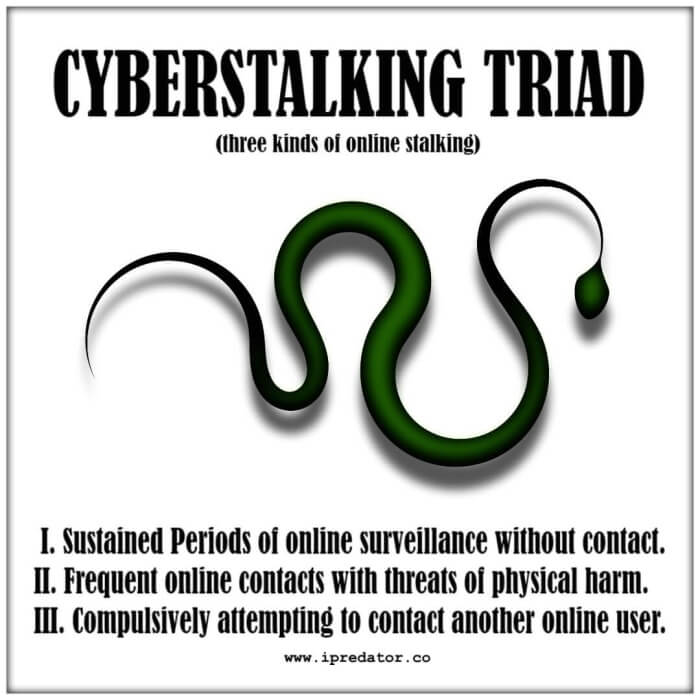
A cyberstalker using cyber surveillance initially does not present a direct physical threat to his/her potential victim but follows the victim’s online activity to gather information on their personal habits and contacts. After sufficient data is compiled, he/she begins to make threats and other forms of verbal intimidation. The anonymity provided to the cyberstalker by online interactions reduces the probability of identification.
This veil of invisibility and low probability of identification makes Cyberstalking far more common than physical stalking. Although cyberstalking might seem harmless by the younger generation or veteran online users, it can easily evolve into psychological and emotional harm. As part of the evolution of cyberstalking and victim inactivity, the veiled hidden harassment may lead to actual physical stalking and/or physical/sexual assault.
Cyberstalkers and Online Predators
Cyberstalkers and online predators target their victims via websites, chat rooms, discussion forums, message boards, blogs, email and text messaging. The availability of free email, website space and frequency of electronic communication usage provides the iPredator with a digital footprint. Having access to this information along with cyberstealth, the increase of cyberstalking in the form of harassment becomes obvious. The cyberstalker starts by quickly doing a Google or search engine search using the person’s alias, real name or email address or any other personal data. Other ways to compile personal information, which one would think innocuous, is by researching a victim’s public profile available at any social media site like Facebook, Instagram and Twitter.
Cyber stalking is a quickly growing form of computer related crime in communities across the country. Cyberstalking is when a person is followed, monitored, harassed and pursued online. Whether the victim is aware or not, their privacy is invaded, their every move is watched and their personal information is slowly compiled. Once aware the stalking is occurring, this form of harassment often disrupts the life of the victim and leaves them feeling very afraid, threatened, anxious and worried.
Cyberstalking usually occurs with women stalked by men, but women at greater rates are increasingly stalking men. Present numbers estimate the gender ratio at 3-1 with women being stalked three times as much. One of the fastest growing segments of victims is children stalked by adult predators, pedophiles and their peer groups.
The obvious difference between physical stalking and cyberstalking is that the cyberstalker does not have to open his or her front door. Everything he/she does can be done online and veiled by anonymity or what this writer has termed Cyberstealth. Cyberstealth, a concept formulated along with iPredator, is a term used to define a method and/or strategy by which iPredators can establish and sustain complete anonymity while they troll and stalk a target. In addition to a stratagem, Cyberstealth is a reality of ICT, which humanity often fails to fathom. Given the internet inherently affords everyone anonymity, cyberstealth used by iPredator ranges from negligible to complex and multi-faceted.
Cyberstalkers need not leave their home to find and harass their targets. Having this anonymity, they have no fear of physical violence or the victim’s loved ones since they cannot be physically touched in cyberspace. They also feel confident legal intervention is not likely given their invisibility. Essentially, Cyberstalkers have a free ticket to act and behave without repercussions. Given this cloak preventing identification, they may be thousands of miles away, as close as a neighbor or even closer being a relative. Their unknown potential, geographic whereabouts or motivations can be a chilling experience.
Cyberstalking and the online predators who engage in these behaviors are growing with every passing year. Although organizations like the Department of Justice and the National Center for Victims of Crime work diligently to educate the public, society remains ignorant of the predators lurking within cyberspace. The reasoning for the public’s refusal to educate themselves and/or children lies in honest denial.
Cyberstalking Prevention
By not affirming these dangers are real, people do not have to be concerned or set boundaries on the information they reveal online. Cyberstalkers and iPredators rely on the public not becoming educated on the necessary steps involved to reduce their potential of becoming their next target. The steps needed for online protection and reasonable security is quite easy and straightforward. Educate yourself and loved ones on iPredator and cyberstalking profiles, set boundaries on personal information disclosed online, refrain from engaging in social exchanges with people you do not know, familiarize yourself with local laws on cyber harassment and always have local law enforcement’s contact information at hand.

Michael Nuccitelli, Psy.D.
Michael Nuccitelli, Psy.D. is a NYS licensed psychologist, cyberpsychology researcher and online safety educator. In 2009, Dr. Nuccitelli finalized his dark side of cyberspace concept called iPredator. Since 2010, he has advised those seeking information about cyberbullying, cyberstalking, cybercriminal minds, internet addiction and his Dark Psychology concept. By day Dr. Nuccitelli is a practicing psychologist, clinical supervisor and owner of MN Psychological Services, PLLC. After work and on the weekends, he volunteers helping online users who have been cyber-attacked. Dr. Nuccitelli’s is always available to interested parties and the media at no cost. This website and everything created by Dr. Nuccitelli is educational, free and public domain.